EST Enrollment Service
The Enrollment over Secure Transport, or EST, is a cryptographic protocol that describes an X.509 certificate management protocol targeting public key infrastructure (PKI) clients. It allows the system to generate a Certificate Signing Request (CSR) to be submitted to a Certificate Autorithy (CA) in order to receive a valid Certificate. EST is described in RFC 7030 and uses HTTPS as transport and leverages TLS for many of its security attributes.
The service downloads the CA certificates storing them in the selected KeystoreService with the alias prefix est-cacerts_.
The generated private KeyPair will be stored in the selected KeystoreService with the alias est-request-key-pair.
The signed certificate received from the EST server will be stored in the KeystoreService with the alias est-enrolled-key-pair.
The service will retry the operation according to the configured parameter Connect Retry-interval, by default every 60 seconds.
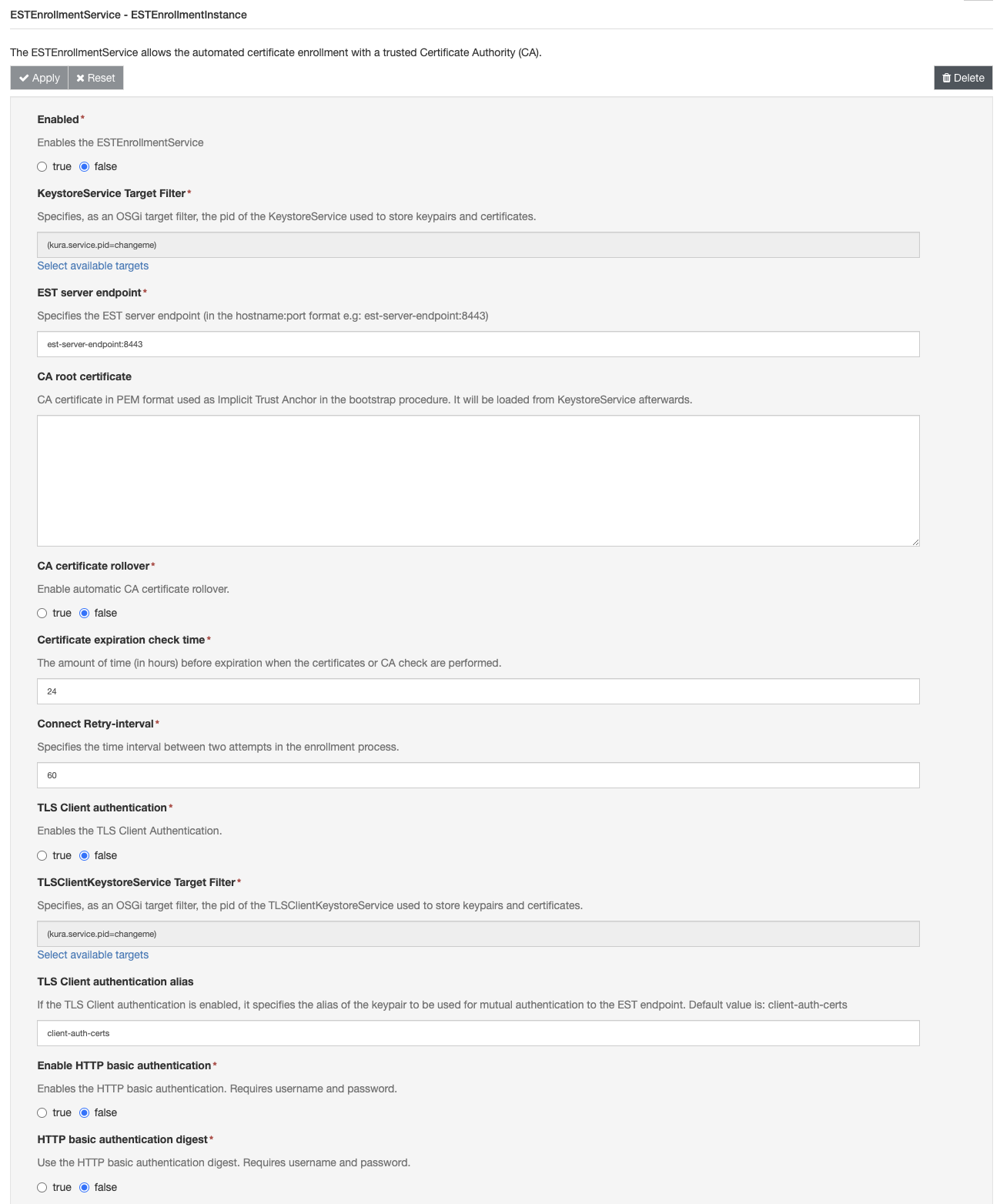
The ESTEnrollmentService component can be configured with the following attributes:
-
Enabled: Enables the ESTEnrollmentService.
-
KeystoreService Target Filter: Specifies, as an OSGi target filter, the pid of the KeystoreService used to store the generated Key Pair, the enrolled certificate, the bootstrap certificate and the server CA certificate.
-
EST server endpoint: Specifies the EST server endpoint (in the hostname:port format e.g: est-server-endpoint:8443).[1]
EST server endpoint URLThe protocol (e.g. http or https) must not be included.
- EST server endpoint label: Optional field which specifies the EST server endpoint label.
- CA root certificate: Certificate Authority root certificate in PEM format used as Implicit Trust Anchor in the bootstrap procedure. It will be loaded from KeystoreService afterwards. [1]
- CA certificate rollover: Enables automatic Certificate Authority certificates rollover.
- Certificate expiration check time: The amount of time (in hours) before expiration when the certificates or CA check are performed.
- Connect Retry-interval: Specifies the time interval between two reconnection attempts in the enrollment process.
- TLS Client authentication: Enables the TLS Client Authentication. The selected KeystoreService must contain a keypair to perform the TLS mutual authentication
- TLS Client authentication KeystoreService Target Filter: Specifies, as an OSGi target filter, the pid of the TLSClientKeystoreService used to load the Key Pair required for the TLS Client Authentication. This keystore is used to perform client mutual authentication when connecting to the selected EST endpoint. This property is valid only when TLS Client authentication is set to true.
- TLS hostname verification: Enable or disable hostname verification.
- TLS Client authentication alias: If the TLS Client authentication property is set to enabled, it specifies the alias of the keypair to be used for mutual authentication to the EST endpoint. Default value is:
client-auth-certs - Enable HTTP basic authentication: Enables the HTTP basic authentication. Requires an username and password.
- HTTP basic authentication digest: Use the HTTP basic authentication digest. Requires username and password.
- HTTP basic authentication username: Username required for HTTP basic authentication.
- HTTP basic authentication password: Password required HTTP basic authentication.
- Proof-of-Possession: Enable Proof-of-Possession. Proof-of-Possession allows the client to prove that it has possession of (i.e., is able to use) the private key corresponding to the public key for which a certificate is requested.
Proof-of-Possession is not supported using TLS Client authentication in conjunction with a PKCS11KeystoreService as TLS Client authentication KeystoreService Target Filter
Note about TLSv1.3EST Proof-of-Possession uses a TLS feature (tls-unique) that is not supported with TLSv1.3. If Proof-of-Possession is enabled, TLSv1.3 will be disabled.
- Client Certificate renew: Enables automatic client certificate renewing.
- Subject Distinguished Name (DN): Distinguished Name (DN) in X.500 format to be used as Subject in the CSR.
- KeyPair generator algorithm: KeyPair generator algorithm to use. At the moment the only supported algorith are EC and RSA
- KeyPair generator algorithm parameter set: KeyPair generator parameter set to use. For RSA this is the size of the key (e.g. 2048 or 4096). For EC this is the name of a standard elliptic curve (e.g. prime256v1).
- CSR signer algorithm: Signer algorithm to use to sign the Certificate Signing Request. Tipically they are SHA256WITHECDSA for EC and SHA256WITHRSA for RSA.
Certificate renewal
The EST Enrollment Service is able to automatically renew the client certificate.
If the Client Certificate renew is set to true, starting from the amount of time (defined by the property Certificate expiration check time) before the certification expiration instant, the service will start the process to renew the certificate using the previous Keypair and the same Subject Distinguished Name (DN)
If the Subject Public Key Info in the certification request is the same as the current client certificate, then the EST server renews the client certificate.
If the public key information in the certification request is different than the current client certificate, then the EST server rekeys the client certificate.
[1] A change in this property triggers a new client bootstrap with a subsequent enrollment
Updated 7 months ago
