Network Configuration
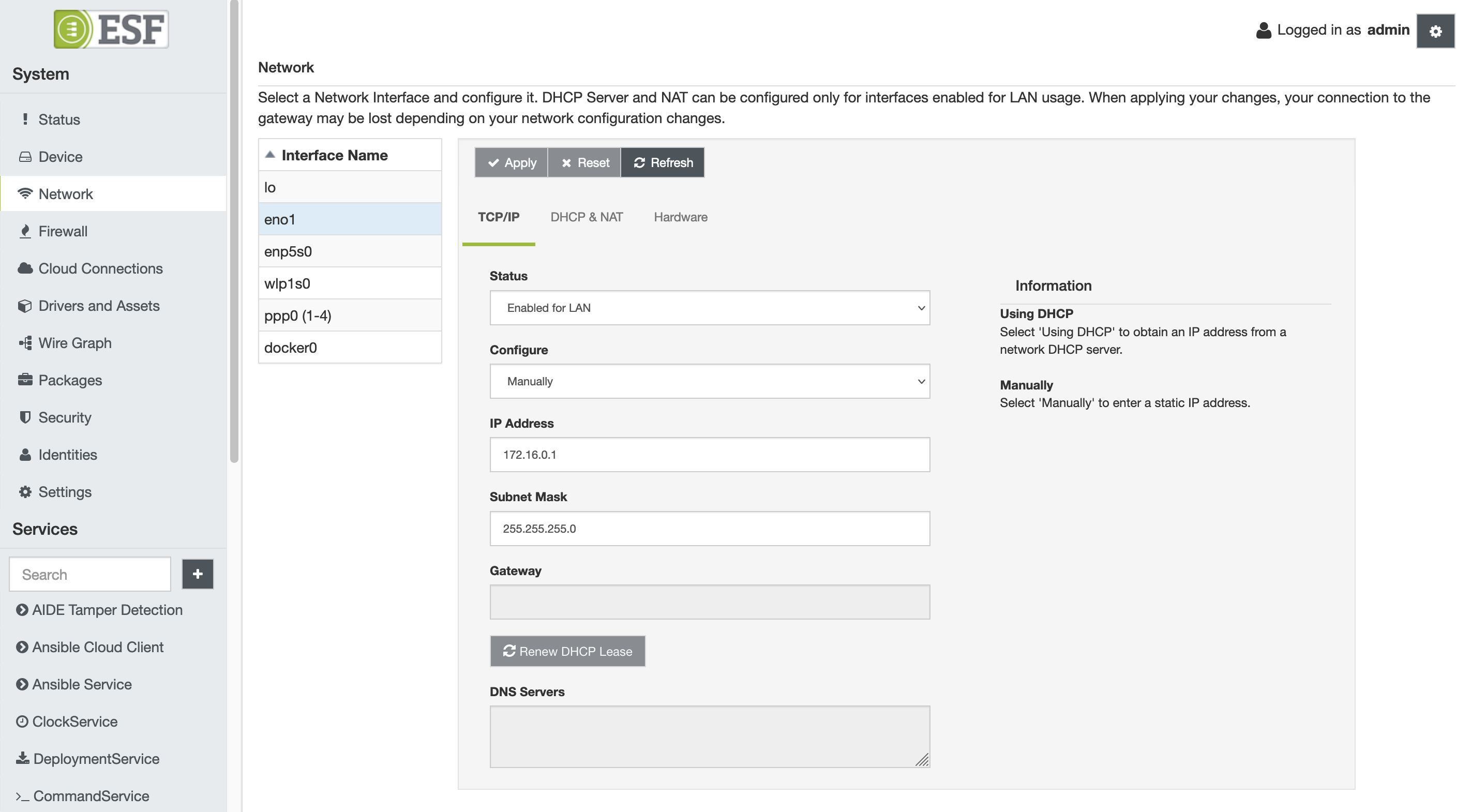
To configure the gateway network interfaces using the ESF Gateway Administration Console, select the Network option located in the System area. With this option selected, the Network display appears with a list of available interfaces. Configuration tabs for the selected interface appear on the right side of the screen. By default, the loopback (lo) interface is selected when the network interfaces are displayed. Choose the desired network interface (e.g., eth0, eth1, wlan0, ppp0) and apply the necessary configuration changes using the tabs on the right. Submit the modified configuration by clicking the Apply button.
In case of typing errors, the Reset button can be used to reload the prior configuration on the screen.
Since the network configuration shown on the screen may not be synchronized with the current state of the system, it can be updated pressing the Refresh button. This can be used also to force the reload of specific parameters like the RSSI or dynamic IP addresses. The refresh procedure reads all the needed parameters from the system and can take several seconds before updating.
Configure TCP/IP FirstIt is recommended that the TCP/IP tab is configured first since it defines how the interface is going to be used.
TCP/IP Configuration
The TCP/IP tab contains the following configuration parameters:
- Status
- Disabled - disables the selected interface (i.e., administratively down).
- Enabled for LAN - designates the interface for a local network. It can be set as a DHCP server for hosts on the local network and can serve as a default gateway for those hosts; however, it cannot be set as an actual gateway interface for this device. That is, packets must be routed from this interface to another interface that is configured as WAN. The interface is automatically brought up at boot.
- Enabled for WAN - designates the interface as a gateway to an external network. The interface is automatically brought up at boot.
- Not Managed - the interface will be ignored by ESF. Users can configure the interface using the networking tools provided by the operating system. This option is available exclusively in the IPv4 tab and applies to both IPv4 and IPv6 configurations.
- WAN Priority - configure the network failover. See here for more details.
- Configure
- Manually - allows manual entry of the IP Address and Netmask fields, if the interface is configured as LAN; allows manual entry of the IP Address, Netmask, Gateway, and DNS Servers fields, if the interface is designated as WAN.
- Using DHCP - configures the interface as a DHCP client obtaining the IP address from a network DHCP server (available only for IPv4).
- Auto - automatically assign an IP address (available only for IPv6).
- Address Generation Mode - defines the method used to automatically generate the IP address with SLAAC (available only for IPv6)
- EUI64 - use EUI-64 method for address generation
- Stable-privacy - use RFC7217 method for address generation
- IP Address - defines the IP address of the interface, if manually configured.
- Subnet Mask - defines the subnet mask of the interface, if manually configured.
- Gateway - specifies the default gateway for the unit. (Required field if the interface is designated as WAN and manually configured.)
- DNS Servers - provides a list of DNS servers, if the interface is designated as WAN and is manually configured.
- Privacy - configure privacy extension for SLAAC (available only for IPv6).
- Disabled: disables the privacy extension.
- Prefer public addresses: use public address for outgoing traffic.
- Prefer temporary addresses: prefer temporary address for outgoing traffic.
If the network interface is Enabled for LAN and manually configured (i.e., not a DHCP client), the DHCP & NAT tab allows the DHCP server to be configured and/or NAT (IP forwarding with masquerading) to be enabled.
More details about the Not Managed interface Status (valid only for non generic profiles)
When a network interface is configured as Not Managed, ESF will ignore it and the configuration will not be touched. The user can configure the interface with the network tools provided by the OS, allowing unusual network setups.
Regarding DNS, both ESF and the external tools store the DNS addresses in the /etc/resolv.conf file. So, if multiple interfaces are configured to get the DNS information and store it in the same file, the device can be misconfigured. To avoid that, the following table presents who is responsible to update the DNS file depending on the network interfaces configurations.
| ESF WAN interface | ESF NotManaged interface | Does ESF manage resolv.conf? |
|---|---|---|
| NO | NO | YES |
| NO | YES | NO |
| YES | NO | YES |
| YES | YES | YES |
So, the only way to configure the DNS addresses with external tools, is to configure at least one interface as Not Managed and not to set any interface as Enabled For Wan using ESF. If at least one WAN interface is configured by ESF, it will take the control of the /etc/resolv.conf/ file. Finally, if any interface is configured in Enabled For Wan or Not Managed mode, ESF will empty the file.
To avoid device misconfigurations when Not Managed interfaces are used, don't use the dns-nameservers directive in the /etc/network/interfaces file. Please add the DNS addresses directly to the /etc/resolv.conf file.
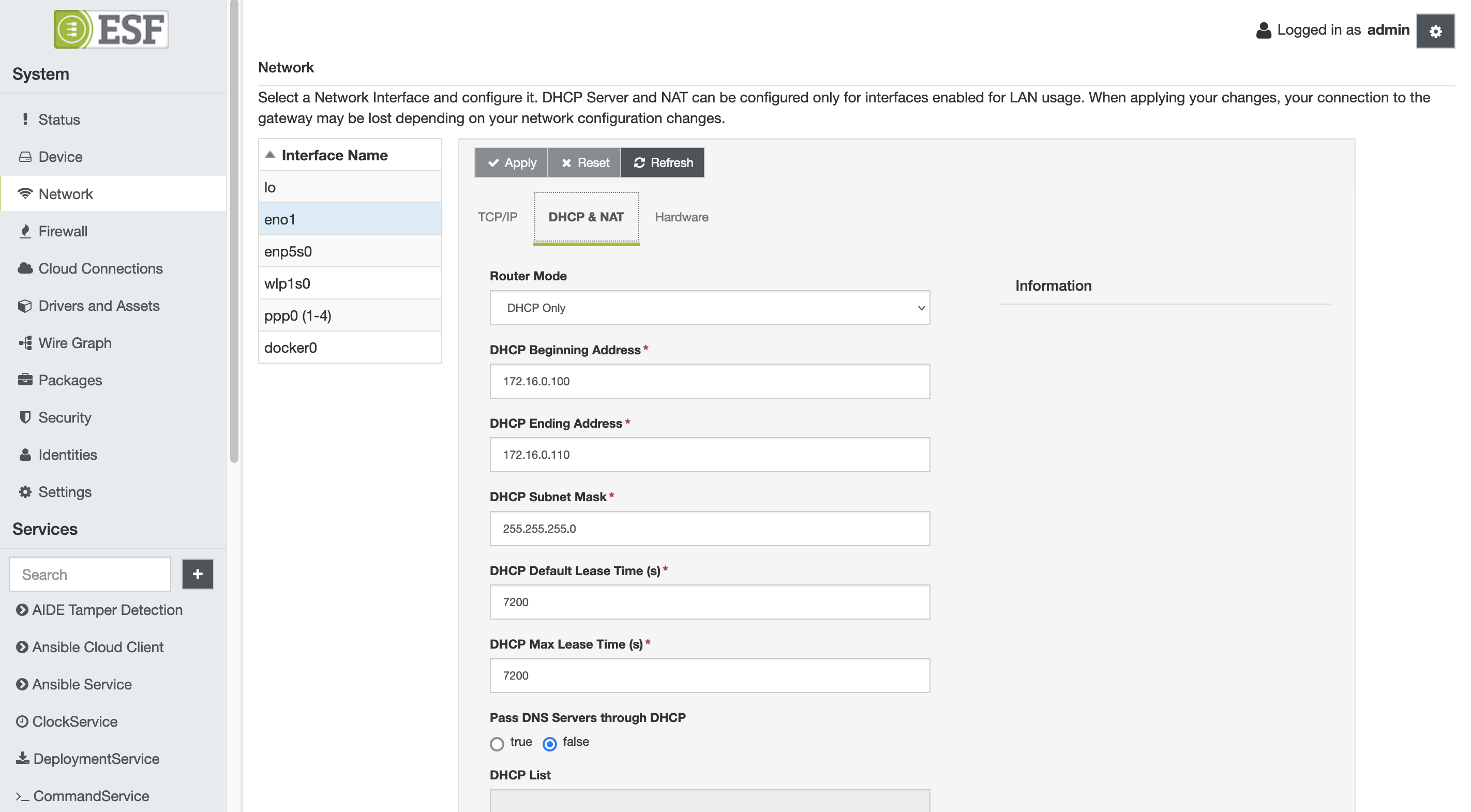
DHCP & NAT Configuration
The DHCP & NAT tab contains the following configuration parameters:
- Router Mode
- DHCP and NAT - indicates that both DHCP server and NAT are enabled.
- DHCP Only - indicates that DHCP server is enabled and NAT is disabled.
- NAT Only - indicates that NAT is enabled and DHCP server is disabled.
- Off - indicates that both DHCP server and NAT are disabled.
- DHCP Beginning Address - specifies the first address of DHCP pool (i.e., first available client IP address).
- DHCP Ending Address - specifies the last address of DHCP pool (i.e., last IP address that can be assigned to a client).
- DHCP Subnet Mask - defines the subnet mask that is assigned to a client.
- DHCP Default Lease Time - sets the default time (in minutes) that the client retains the provided IP address. It must be greater than 0.
- DHCP Max Lease Time - sets the maximum time (in minutes) that the client retains the provided IP address. It must be greater than 0.
- Pass DNS Servers through DHCP - enables DNS Proxy (i.e., passing DNS servers through DHCP).
If NAT is enabled and there is another interface designated as WAN (e.g., ppp0), the following iptables rules are added to the custom automatic NAT service rules section of the /etc/init.d/firewall script:
# custom automatic NAT service rules (if NAT option is enabled for LAN interface)
iptables -t nat -A POSTROUTING -o ppp0 -j MASQUERADE
iptables -A FORWARD -i ppp0 -o eth0 -m state --state RELATED,ESTABLISHED -j ACCEPT
iptables -A FORWARD -i eth0 -o ppp0 -j ACCEPTAlso, IP forwarding is enabled in the kernel as follows:
# allow fowarding if any masquerade is defined
echo 1 > /proc/sys/net/ipv4/ip_forwardThe rules shown above create an Overloaded (i.e., many-to-one) NAT. This type of network address translation maps multiple IP addresses on the LAN side to a single IP address on the WAN side, allowing internet access from hosts on a local network via a gateway (WAN) interface. Note that for NAT rules to be added, it is insufficient to enable NATing through the DHCP & NAT tab of the LAN interface; there must also be another interface designated as WAN.
Network Linux Configuration
When applying a new network configuration, ESF changes the configuration files of the Linux networking subsystem. Please read the following note before proceeding with manual changes of the Linux networking configuration.
Avoid Conflicting Configuration ChangesEurotech does NOT recommend performing manual editing of the Linux networking configuration files when the gateway configuration is being managed through ESF. While Linux may correctly accept manual changes, ESF may not be able to interpret the new configuration resulting in an inconsistent state.
IPv6 Addressing Modes
When the Configure option in the IPv6 tab is set to Using DHCPv6, the network interface obtains its IPv6 address and DNS information from the DHCPv6 server. However, it is important to note that the default gateway is not supplied by the network in this mode, even if the interface is designated as Enabled for WAN.
To retrieve the default gateway, set the Configure option to SLAAC. In this configuration, the default gateway is obtained through Router Advertisements (RA) sent as part of the Neighbor Discovery Protocol (NDP).
If the interface is configured in Using DHCPv6 mode, ensure that UDP port 546 is open in the IPv6 firewall so the DHCPv6 client can receive replies.
It is important to note that the actual behavior is influenced by the router's configuration. Router Advertisements include two flags, M (Managed) and O (Other), which determine whether hosts should utilize SLAAC, DHCPv6, or a combination of both. The table below summarizes these configurations:
| Flags (M/O) | Address source | DNS Source | Default Gateway Source | Description |
|---|---|---|---|---|
| M=0, O=0 | SLAAC | RA | RA | Pure SLAAC environment. The router provides all required configuration through Router Advertisements. No DHCPv6 services are used. |
| M=0, O=1 | SLAAC | DHCPv6 | RA | SLAAC for addressing, with DHCPv6 used only for “other configuration such as DNS. A mixed or “hybrid” setup. |
| M=1, O=0 | DHCPv6 | DHCPv6 | RA | Fully managed IPv6 network. Hosts rely on DHCPv6 for address and configuration details. |
| M=1, O=1 | DHCPv6 | DHCPv6 | RA | Same as M=1/O=0: a stateful, DHCPv6-managed network. Both flags instruct hosts to use DHCPv6 for address assignment and additional configuration. |
Network Configuration properties
The Network configuration can be modified using the ESF Gateway Administration Console, as described above, the Configuration Service or appling a proper snapshot.
The following table describes all the properties related to the Network Configuration. The network configuration pid is org.eclipse.kura.net.admin.NetworkConfigurationService.
Common properties
Name | Type | Description | Default Value |
|---|---|---|---|
net.interfaces | String | Comma-separated list of the interface names in the device | |
net.interface. | String | The type of the network interface; possible values are: ETHERNET, WIFI, MODEM, VLAN, LOOPBACK and UNKNOWN | UNKNOWN |
net.interface. | String | For wifi interfaces, specify the modality; possible values are INFRA, MASTER and UNKNOWN | UNKNOWN |
net.interface. | Boolean | Enable the NAT feature | false |
net.interface. | Integer | Enable the Promiscuous Mode; possible values are: -1 (System default), 0 (Disabled), 1 (Enabled) | -1 |
IPv4 properties
Name | Type | Description | Default Value |
|---|---|---|---|
net.interface. | String | The status of the interface for the IPv4 configuration; possibile values are: netIPv4StatusDisabled, netIPv4StatusUnmanaged, netIPv4StatusL2Only1 , | netIPv4StatusDisabled`(see note below) |
net.interface. | Integer | (NetworkManager only) Priority used to determine which interface select as primary WAN. Allowed values range from -1 to 2147483647, inclusive. See Network Failover for further details | -1 |
net.interface. | String | The IPv4 address assigned to the network interface | |
net.interface. | Short | The IPv4 netmask assigned to the network interface | -1 |
net.interface. | String | The IPv4 address of the default gateway | |
net.interface. | String | Comma-separated list of dns servers | |
net.interface. | Integer | The Maximum Transition Unit (MTU) for this interface |
Configure TCP/IP First
NoteFor physical interfaces the default status is
netIPv4StatusDisabled. For virtual ones, instead, the default status is defined by thekura.net.virtual.devices.configproperty in thekura.propertiesfile.
IPv4 DHCP Server properties
| Name | Type | Description | Default Value |
|---|---|---|---|
net.interface.<interface>.config.dhcpServer4.enabled | Boolean | Specify if the DHCP server is enabled | false |
net.interface.<interface>.config.dhcpServer4.rangeStart | String | First IP address available for clients | |
net.interface.<interface>.config.dhcpServer4.rangeEnd | String | Last IP address available for clients | |
net.interface.<interface>.config.dhcpServer4.defaultLeaseTime | Integer | The default lease time | -1 |
net.interface.<interface>.config.dhcpServer4.maxLeaseTime | Integer | The maximum lease time | -1 |
net.interface.<interface>.config.dhcpServer4.prefix | Short | The netmask for the available IP addresses | -1 |
net.interface.<interface>.config.dhcpServer4.passDns | Boolean | Specify if the DNS server addresses has to be passed through DHCP | false |
IPv4 DHCP Client properties
| Name | Type | Description | Default Value |
|---|---|---|---|
net.interface.<interface>.config.dhcpClient4.enabled | Boolean | Specify if the DHCP client is enabled | false |
IPv6 properties
Name | Type | Description | Default Value |
|---|---|---|---|
net.interface. | String | The status of the interface for the IPv6 configuration; possibile values are: netIPv6StatusDisabled, netIPv6StatusUnmanaged, | netIPv6StatusDisabled (see note below) |
net.interface. | Integer | (NetworkManager only) Priority used to determine which interface select as primary WAN. Allowed values range from -1 to 2147483647, inclusive. See Network Failover for further details | -1 |
net.interface. | String | The IPv6 configuration method; possible values are: netIPv6MethodAuto, netIPv6MethodDhcp, netIPv6MethodManual. | netIPv6MethodAuto |
net.interface. | String | The IPv6 address assigned to the network interface | |
net.interface. | Short | The IPv6 netmask assigned to the network interface | -1 |
net.interface. | String | The IPv6 address of the default gateway | |
net.interface. | String | Comma-separated list of dns servers | |
net.interface. | String | The IPv6 address generation mode; possible values are EUI64, STABLE_PRIVACY | |
net.interface. | String | The IPv6 Privacy Extensions for SLAAC; possible values are DISABLED, ENABLED_PUBLIC_ADD, ENABLED_TEMP_ADD | |
net.interface. | Integer | The Maximum Transition Unit (MTU) for Ipv6 traffic on this interface. Requires NetworkManager 1.40 or newer |
NoteFor physical interfaces the default status is
netIPv6StatusDisabled. For virtual ones, instead, the default status is defined by thekura.net.virtual.devices.configproperty in thekura.propertiesfile.
WiFi Master (Access Point) properties
Name | Type | Description | Default Value |
|---|---|---|---|
net.interface. | String | The driver used for the connection | |
net.interface. | Password | The password for the access point | |
net.interface. | String | The SSID of the access point | |
net.interface. | String | The security protocol for the wireless network; possible values are NONE, SECURITY_WEP, | NONE |
net.interface. | String | The mode of the wireless connection; for the access point mode set it to MASTER | MASTER |
net.interface. | String | The channel to be used for the access point | 1 |
net.interface. | String | Specify the 802.11 radio mode; possible values are RADIO_MODE_80211a, RADIO_MODE_80211b, RADIO_MODE_80211g, RADIO_MODE_80211nHT20, RADIO_MODE_80211_AC | RADIO_MODE_80211b |
net.interface. | Boolean | Specify if the SSID broadcast is ignored | false |
net.interface. | String | Group ciphers, possible values are CCMP, TKIP, and CCMP_TKIP | CCMP_TKIP |
net.interface. | String | Pairwise ciphers, possible values are CCMP, TKIP, and CCMP_TKIP | CCMP_TKIP |
WiFi Infra (Station Mode) properties
Name | Type | Description | Default Value |
|---|---|---|---|
net.interface. | String | The SSID of the wireless network to connect to | |
net.interface. | String | The channel of the wireless network to connect to | 1 |
net.interface. | String | Set the background scans; possible values have the form
| |
net.interface. | Password | The password for the wireless network | |
net.interface. | Boolean | Specify if a scan for SSID is required before attempting to associate | false |
net.interface. | String | The mode of the wireless connection; for station mode set to INFRA | INFRA |
net.interface. | Boolean | Enable pinging the access point after connection is established | false |
net.interface. | String | The driver used for the connection | |
net.interface. | String | The security protocol for the wireless network; possible values are SECURITY_NONE, SECURITY_WEP, | SECURITY_NONE |
net.interface. | String | Group ciphers, possible values are CCMP, TKIP, and CCMP_TKIP | CCMP_TKIP |
net.interface. | String | Pairwise ciphers, possible values are CCMP, TKIP, and CCMP_TKIP | CCMP_TKIP |
Cellular Modem properties
Name | Type | Description | Default Value |
|---|---|---|---|
net.interface. | Boolean | Enable the interface | false |
net.interface. | Integer | The idle option of the PPP daemon | 95 |
net.interface. | String | The username used for the connection | |
net.interface. | Password | The password used for the connection | |
net.interface. | String | The PdP type; possible values are IP, PPP and IPv6 | IP |
net.interface. | Integer | The maxfail option of the PPP daemon | 5 |
net.interface. | String | The authentication type; possible values are NONE, AUTO, CHAP and PAP | NONE |
net.interface. | Integer | the lcp-echo-interval option of the PPP daemon | 0 |
net.interface. | String | The active-filter option of the PPP daemon | inbound |
net.interface. | Integer | The lcp-echo-failure option of the PPP daemon | 0 |
net.interface. | Boolean | Enable the LTE diversity antenna | false |
net.interface. | Integer | The modem reset timeout in minutes | 5 |
net.interface. | Boolean | Enable the GPS device in the modem if available | false |
net.interface. | String | Select the GPS mode to activate for the modem if available | kuraModemGpsModeUnmanaged |
net.interface. | Boolean | The persist option of the PPP daemon | true |
net.interface. | String | The modem Access Point Name | |
net.interface. | String | The dial string used for connecting to the APN | |
net.interface. | Integer | The holdoff option of the PPP daemon (in seconds) | |
net.interface. | Integer | Assigned ppp interface number | 0 |
GPS Mode
The GPS mode can be set to one of the following values:
kuraModemGpsModeUnmanaged: the GPS device of the modem will be setup but not directly managed, therefore freeing the serial port for other services to use. This can be used in order to perform the setup of the GPS and then have another service (likegpsd) parse the NMEA strings in order to extract the position informations. This is the default value.kuraModemGpsModeManagedGps: the GPS device of the modem will be setup and directly managed (typically by ModemManager) therefore the serial port won't be available for other services to use.
For older versions compatibility, if the net.interface.<interface>.config.gpsMode property is not set, the GPS mode will be automatically set to the kuraModemGpsModeUnmanaged equivalent.
VLAN properties
Name | Type | Description | Default Value |
|---|---|---|---|
net.interface. | String | Physical interface Vlan is bound to | |
net.interface. | Integer | Vlan tag identifier, between 0 and 4094 | |
net.interface. | String | Incoming traffic priorities in the format from:to, as comma separated pairs of unsigned integers (Optional) | |
net.interface. | String | Outgoing traffic priorities in the format from:to, as comma separated pairs of unsigned integer (Optional) | |
net.interface. | String | Configuration flags, between 0 and 15 (Optional) | 1 |
802.1x properties
Name | Type | Description |
|---|---|---|
| String | The EAP method to be used when authenticating to the network with 802.1x. Supported methods: "Kura8021xEapTls", "Kura8021xEapPeap", "Kura8021xEapTtls". |
| String | Specifies the "phase 2" inner authentication method when an EAP method that uses an inner TLS tunnel is specified in the "eap" property. Supported methods: "Kura8021xInnerAuthNone", "Kura8021xInnerAuthMschapv2". |
| String | Identity string for EAP authentication methods. Typically the user's user or login name. |
| String | Password used for EAP authentication methods. |
| String | Name referring to the corresponding Kura keystore entry containing the client certificate if used by the EAP method specified in the "eap" property. Typically is set to the same name as the |
| String | Name referring to the corresponding Kura keystore entry containing the private key when the "eap" property is set to "Kura8021xEapTls". Typically is set to the same name as the |
| String | Name referring to the corresponding Kura keystore entry containing the CA certificate if used by the EAP method specified in the "eap" property. This parameter is optional but this allows man-in-the-middle attacks and is NOT recommended. |
| String | Anonymous identity string for EAP authentication methods. Used as the unencrypted identity with EAP types that support different tunneled identity like EAP-TTLS (Optional) |
Network Configuration recipes
This section presents some snapshot examples to perform basic operations on networking. The snippets can be modified adapting them to the required configuration (i.e. changing the interface name in the property to be applied).
Be aware that an inconsitent or wrong configuration can compromise the network functionality of the gateway. Try the new configuration on a test device before appling it in a production environment!
Moreover, if a property is not present in the new snapshot, the old value is used for the configuration. So, the best practice is to set all the needed properties in the snapshot.
Disable a network interface
<?xml version="1.0" encoding="UTF-8"?>
<esf:configurations xmlns:esf="http://eurotech.com/esf/2.0" xmlns:ocd="http://www.osgi.org/xmlns/metatype/v1.2.0">
<esf:configuration pid="org.eclipse.kura.net.admin.NetworkConfigurationService">
<esf:properties>
<esf:property array="false" encrypted="false" name="net.interface.enp5s0.type" type="String">
<esf:value>ETHERNET</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.enp5s0.config.ip4.status" type="String">
<esf:value>netIPv4StatusDisabled</esf:value>
</esf:property>
</esf:properties>
</esf:configuration>
</esf:configurations>Configure an ethernet interface for WAN with DHCP client enabled and custom DNS server
<?xml version="1.0" encoding="UTF-8"?>
<esf:configurations xmlns:esf="http://eurotech.com/esf/2.0" xmlns:ocd="http://www.osgi.org/xmlns/metatype/v1.2.0">
<esf:configuration pid="org.eclipse.kura.net.admin.NetworkConfigurationService">
<esf:properties>
<esf:property array="false" encrypted="false" name="net.interface.enp5s0.type" type="String">
<esf:value>ETHERNET</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.enp5s0.config.ip4.dnsServers" type="String">
<esf:value>1.2.3.4</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.enp5s0.config.dhcpClient4.enabled" type="Boolean">
<esf:value>true</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.enp5s0.config.dhcpServer4.enabled" type="Boolean">
<esf:value>false</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.enp5s0.config.ip4.status" type="String">
<esf:value>netIPv4StatusEnabledWAN</esf:value>
</esf:property>
</esf:properties>
</esf:configuration>
</esf:configurations>Configure an ethernet interface for LAN with DHCP server enabled and NAT disabled
<?xml version="1.0" encoding="UTF-8"?>
<esf:configurations xmlns:esf="http://eurotech.com/esf/2.0" xmlns:ocd="http://www.osgi.org/xmlns/metatype/v1.2.0">
<esf:configuration pid="org.eclipse.kura.net.admin.NetworkConfigurationService">
<esf:properties>
<esf:property array="false" encrypted="false" name="net.interface.enp5s0.type" type="String">
<esf:value>ETHERNET</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.enp5s0.config.ip4.dnsServers" type="String">
<esf:value/>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.enp5s0.config.dhcpClient4.enabled" type="Boolean">
<esf:value>false</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.enp5s0.config.ip4.status" type="String">
<esf:value>netIPv4StatusEnabledLAN</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.enp5s0.config.dhcpServer4.rangeEnd" type="String">
<esf:value>192.168.4.110</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.enp5s0.config.dhcpServer4.enabled" type="Boolean">
<esf:value>true</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.enp5s0.config.dhcpServer4.defaultLeaseTime" type="Integer">
<esf:value>900</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.enp5s0.config.dhcpServer4.prefix" type="Short">
<esf:value>24</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.enp5s0.config.dhcpServer4.passDns" type="Boolean">
<esf:value>true</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.enp5s0.config.dhcpServer4.rangeStart" type="String">
<esf:value>192.168.4.100</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.enp5s0.config.dhcpServer4.maxLeaseTime" type="Integer">
<esf:value>900</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.enp5s0.config.ip4.address" type="String">
<esf:value>192.168.4.1</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.enp5s0.config.ip4.prefix" type="Short">
<esf:value>24</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.enp5s0.config.ip4.gateway" type="String">
<esf:value/>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.enp5s0.config.nat.enabled" type="Boolean">
<esf:value>false</esf:value>
</esf:property>
</esf:properties>
</esf:configuration>
</esf:configurations>Configure a wireless interface as access point with DHCP server and NAT enabled
<?xml version="1.0" encoding="UTF-8"?>
<esf:configurations xmlns:esf="http://eurotech.com/esf/2.0" xmlns:ocd="http://www.osgi.org/xmlns/metatype/v1.2.0">
<esf:configuration pid="org.eclipse.kura.net.admin.NetworkConfigurationService">
<esf:properties>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.type" type="String">
<esf:value>WIFI</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.ip4.status" type="String">
<esf:value>netIPv4StatusEnabledLAN</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.ip4.gateway" type="String">
<esf:value/>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.ip4.dnsServers" type="String">
<esf:value/>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.ip4.prefix" type="Short">
<esf:value>24</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.ip4.address" type="String">
<esf:value>172.16.1.1</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.dhcpClient4.enabled" type="Boolean">
<esf:value>false</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.dhcpServer4.rangeStart" type="String">
<esf:value>172.16.1.100</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.dhcpServer4.maxLeaseTime" type="Integer">
<esf:value>900</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.dhcpServer4.defaultLeaseTime" type="Integer">
<esf:value>900</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.dhcpServer4.rangeEnd" type="String">
<esf:value>172.16.1.110</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.dhcpServer4.prefix" type="Short">
<esf:value>24</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.dhcpServer4.enabled" type="Boolean">
<esf:value>true</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.dhcpServer4.passDns" type="Boolean">
<esf:value>true</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.nat.enabled" type="Boolean">
<esf:value>true</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.wifi.mode" type="String">
<esf:value>MASTER</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.wifi.master.driver" type="String">
<esf:value>nl80211</esf:value>
</esf:property>
<esf:property array="false" encrypted="true" name="net.interface.wlp1s0.config.wifi.master.passphrase" type="Password">
<esf:value>ZW5hYmxlbWVwbGVhc2U=</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.wifi.master.ssid" type="String">
<esf:value>kura_gateway_19</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.wifi.master.securityType" type="String">
<esf:value>SECURITY_WPA2</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.wifi.master.mode" type="String">
<esf:value>MASTER</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.wifi.master.channel" type="String">
<esf:value>11</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.wifi.master.radioMode" type="String">
<esf:value>RADIO_MODE_80211g</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.wifi.master.ignoreSSID" type="Boolean">
<esf:value>false</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.wifi.master.pairwiseCiphers" type="String">
<esf:value>CCMP</esf:value>
</esf:property>
</esf:properties>
</esf:configuration>
</esf:configurations>Configure a wireless interface as station mode with DHCP client enabled
<?xml version="1.0" encoding="UTF-8"?>
<esf:configurations xmlns:esf="http://eurotech.com/esf/2.0" xmlns:ocd="http://www.osgi.org/xmlns/metatype/v1.2.0">
<esf:configuration pid="org.eclipse.kura.net.admin.NetworkConfigurationService">
<esf:properties>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.type" type="String">
<esf:value>WIFI</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.ip4.status" type="String">
<esf:value>netIPv4StatusEnabledLAN</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.ip4.dnsServers" type="String">
<esf:value/>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.dhcpClient4.enabled" type="Boolean">
<esf:value>true</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.dhcpServer4.enabled" type="Boolean">
<esf:value>false</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.wifi.mode" type="String">
<esf:value>INFRA</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.wifi.infra.ssid" type="String">
<esf:value>MyWirelessNetwork</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.wifi.infra.bgscan" type="String">
<esf:value/>
</esf:property>
<esf:property array="false" encrypted="true" name="net.interface.wlp1s0.config.wifi.infra.passphrase" type="Password">
<esf:value>MyPasswordBase64</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.wifi.infra.ignoreSSID" type="Boolean">
<esf:value>false</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.wifi.infra.mode" type="String">
<esf:value>INFRA</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.wifi.infra.pingAccessPoint" type="Boolean">
<esf:value>false</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.wifi.infra.driver" type="String">
<esf:value>nl80211</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.wlp1s0.config.wifi.infra.securityType" type="String">
<esf:value>SECURITY_WPA2</esf:value>
</esf:property>
</esf:properties>
</esf:configuration>
</esf:configurations>Enable a cellular interface
<?xml version="1.0" encoding="UTF-8"?>
<esf:configurations xmlns:esf="http://eurotech.com/esf/2.0" xmlns:ocd="http://www.osgi.org/xmlns/metatype/v1.2.0">
<esf:configuration pid="org.eclipse.kura.net.admin.NetworkConfigurationService">
<esf:properties>
<esf:property array="false" encrypted="false" name="net.interface.1-1.type" type="String">
<esf:value>MODEM</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.1-1.config.ip4.status" type="String">
<esf:value>netIPv4StatusEnabledWAN</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.1-1.config.ip4.dnsServers" type="String">
<esf:value/>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.1-1.config.dhcpClient4.enabled" type="Boolean">
<esf:value>true</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.1-1.config.dhcpServer4.enabled" type="Boolean">
<esf:value>false</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.1-1.config.idle" type="Integer">
<esf:value>95</esf:value>
</esf:property>
<esf:property array="false" encrypted="true" name="net.interface.1-1.config.password" type="Password">
<esf:value/>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.1-1.config.pdpType" type="String">
<esf:value>IP</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.1-1.config.ipAddress" type="String">
<esf:value/>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.1-1.config.maxFail" type="Integer">
<esf:value>5</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.1-1.config.authType" type="String">
<esf:value>NONE</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.1-1.config.lcpEchoInterval" type="Integer">
<esf:value>0</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.1-1.config.enabled" type="Boolean">
<esf:value>true</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.1-1.config.activeFilter" type="String">
<esf:value>inbound</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.1-1.config.lcpEchoFailure" type="Integer">
<esf:value>0</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.1-1.config.diversityEnabled" type="Boolean">
<esf:value>false</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.1-1.config.resetTimeout" type="Integer">
<esf:value>5</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.1-1.config.gpsEnabled" type="Boolean">
<esf:value>false</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.1-1.config.persist" type="Boolean">
<esf:value>true</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.1-1.config.dialString" type="String">
<esf:value>atd*99***2#</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.1-1.config.apn" type="String">
<esf:value>web.omnitel.it</esf:value>
</esf:property>
</esf:properties>
</esf:configuration>
</esf:configurations>Create a VLAN
<?xml version="1.0" encoding="UTF-8"?><esf:configurations xmlns:esf="http://eurotech.com/esf/2.0" xmlns:ocd="http://www.osgi.org/xmlns/metatype/v1.2.0">
<esf:configuration pid="org.eclipse.kura.net.admin.NetworkConfigurationService">
<esf:properties>
<esf:property array="false" encrypted="false" name="net.interfaces" type="String">
<esf:value>wlan0,lo,ens33,vlanFull,ens34</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.vlanFull.config.dhcpServer4.enabled" type="Boolean">
<esf:value>false</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.vlanFull.config.nat.enabled" type="Boolean">
<esf:value>false</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.vlanFull.config.dhcpClient4.enabled" type="Boolean">
<esf:value>false</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.vlanFull.type" type="String">
<esf:value>VLAN</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.vlanFull.config.ip4.status" type="String">
<esf:value>netIPv4StatusEnabledLAN</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.vlanFull.config.vlan.parent" type="String">
<esf:value>ens33</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.vlanFull.config.vlan.id" type="Integer">
<esf:value>41</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.vlanFull.config.vlan.flags" type="Integer">
<esf:value>1</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.vlanFull.config.vlan.ingress" type="String">
<esf:value>1:2,3:4</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.vlanFull.config.vlan.egress" type="String">
<esf:value>5:6</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.vlanFull.config.ip4.address" type="String">
<esf:value>192.168.41.100</esf:value>
</esf:property>
<esf:property array="false" encrypted="false" name="net.interface.vlanFull.config.ip4.prefix" type="Short">
<esf:value>24</esf:value>
</esf:property>
</esf:properties>
</esf:configuration>
</esf:configurations>Updated 6 months ago
