Keystores Management
The framework effectively manages various types of cryptographic keys and certificates. To streamline interaction with these objects, the ESF offers a KeystoreService API and a dedicated section in the ESF Web UI that displays all available KeystoreService instances.
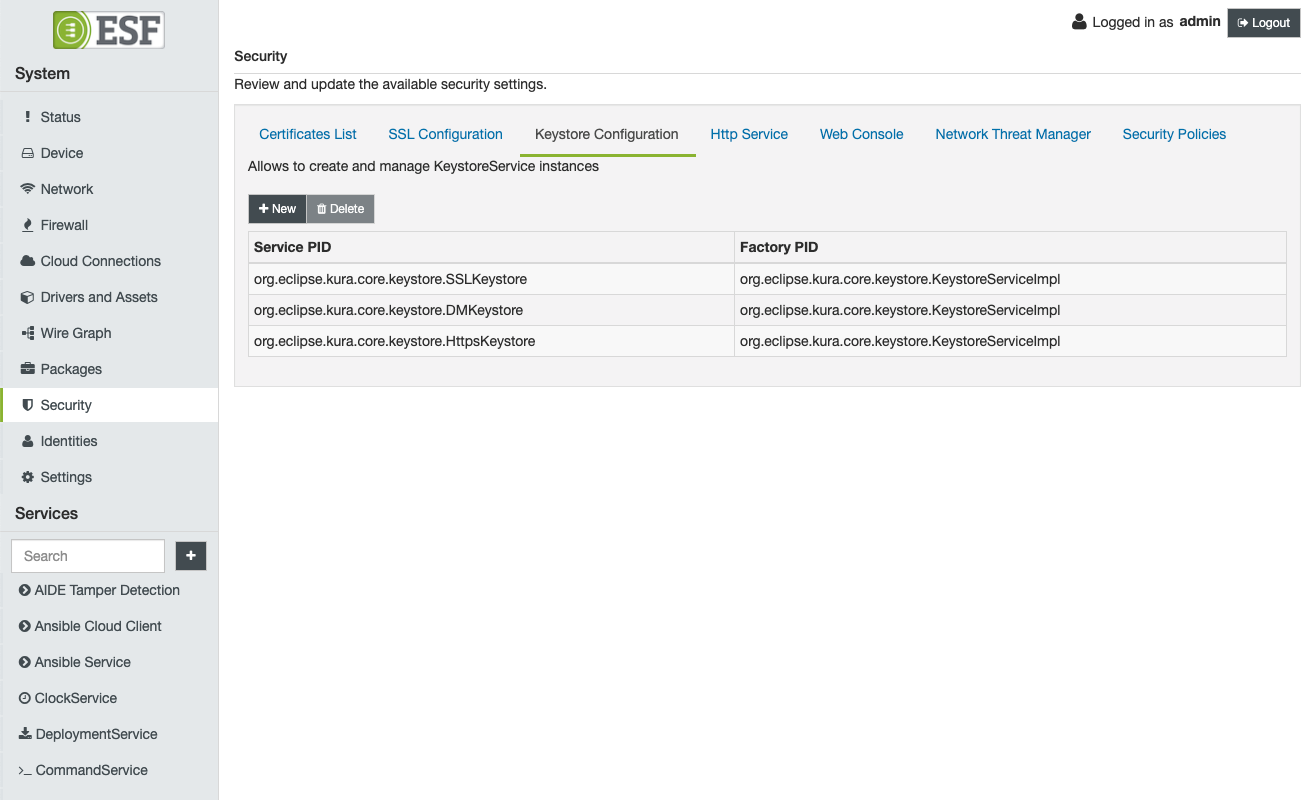
Users with Security permissions can access the Keystore Configuration section from the Security area. Here, they will find a list of all the keystores managed by the framework, along with their corresponding Service PID, which is used by other components to reference the selected keystore. Additionally, the UI displays the Factory PID, indicating the specific KeystoreService API implementation providing the service to the framework.
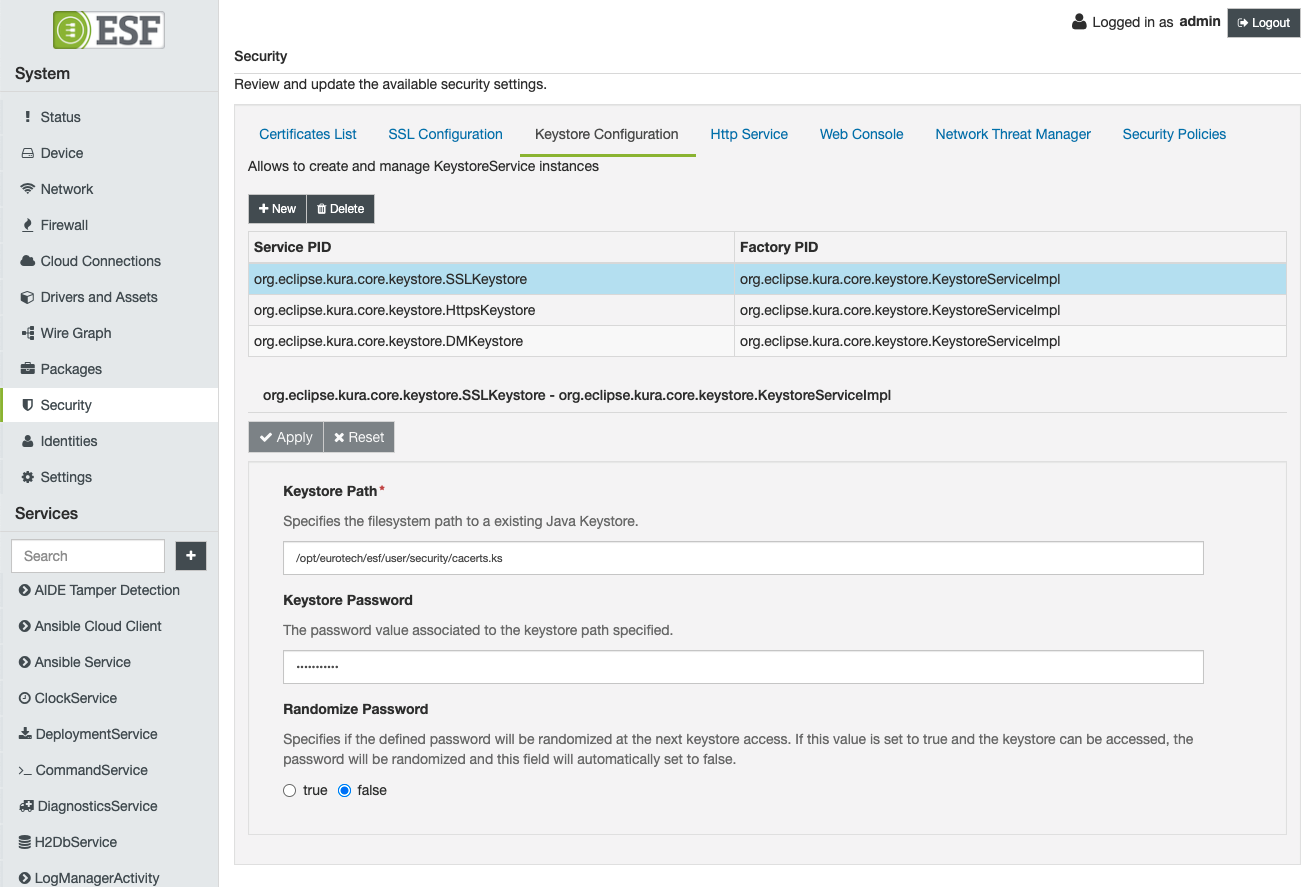
To modify the configuration of a specific keystore service instance, the user can select one of the available rows to access the corresponding keystore service configuration.
Default KeystoreService factories
The following KeystoreService factories are available:
FilesystemKeystoreServiceImpl
The org.eclipse.kura.core.keystore.FilesystemKeystoreServiceImpl factory offers a KeystoreService implementation that stores private keys and certificates in a file. Users can customize the following options:
- Keystore Path: Specifies the path in the filesystem. If the keystore file does not exist, a new file will be created. This value cannot be empty.
- Keystore Password: The password associated with the keystore.
- Randomize Password: A boolean flag that allows the user to indicate whether the keystore password should be randomized at the next framework boot. If set to true, the framework will attempt to access the specified keystore and randomize the password. The new password will be saved in the framework snapshot. Once successfully randomized, the flag will be automatically set to false by the framework.
PKCS11KeystoreServiceImpl
The org.eclipse.kura.core.keystore.PKCS11KeystoreServiceImpl factory provides a KeystoreService implementation that enables access to a PKCS11 token through the SunPKCS11 implementation.
Currently, this type of KeystoreService only offers read-only access to the underlying token; operations such as adding or removing entries will not succeed.
Entries provided by a PKCS11KeystoreServiceImpl can be utilized for SSL authentication.
The available configuration options align closely with the parameters specified by the SunPKCS11 implementation. For more information, refer to the official documentation.
Notably, the official documentation includes a section detailing how PKCS11 objects are mapped to Java KeyStore entries.
The only required parameter is the PKCS11 Implementation Library Path. It is often necessary to specify the token user PIN using the Pin parameter as well.
The configuration parameters correspond to the SunPKCS11 provider parameters in the following manner:
| Kura Parameter | SunPKCS11 Parameter | Notes |
|---|---|---|
| Slot | slot | |
| Slot List Index | slotListIndex | |
| Enabled Mechanisms | enabledMechanisms | The curly braces must be omitted |
| Disabled Mechanisms | disabledMechanisms | The curly braces must be omitted. |
| Attributes | attributes | The value of this field will be appended to the provider configuration. |
Default KeystoreService instancies
The following KeystoreService instances are included in a default ESF installation:
- org.eclipse.kura.crypto.CryptoService: This is a keystore instance managed by the ESF security manager. It cannot be deleted, and users can interact with it to manage the application certificates used for bundle signing.
- SSLKeystore: A filesystem keystore utilized for secure SSL communication.
- DMKeystore: A filesystem keystore that stores the certificates used by the framework to verify device management messages received from the management cloud platform.
- HttpsKeystore: A filesystem keystore that contains the key pair used by the ESF web server for SSL setup, as well as the certificates of the CAs used for user certificate-based authentication.
Updated 7 months ago
