Network Threat Manager
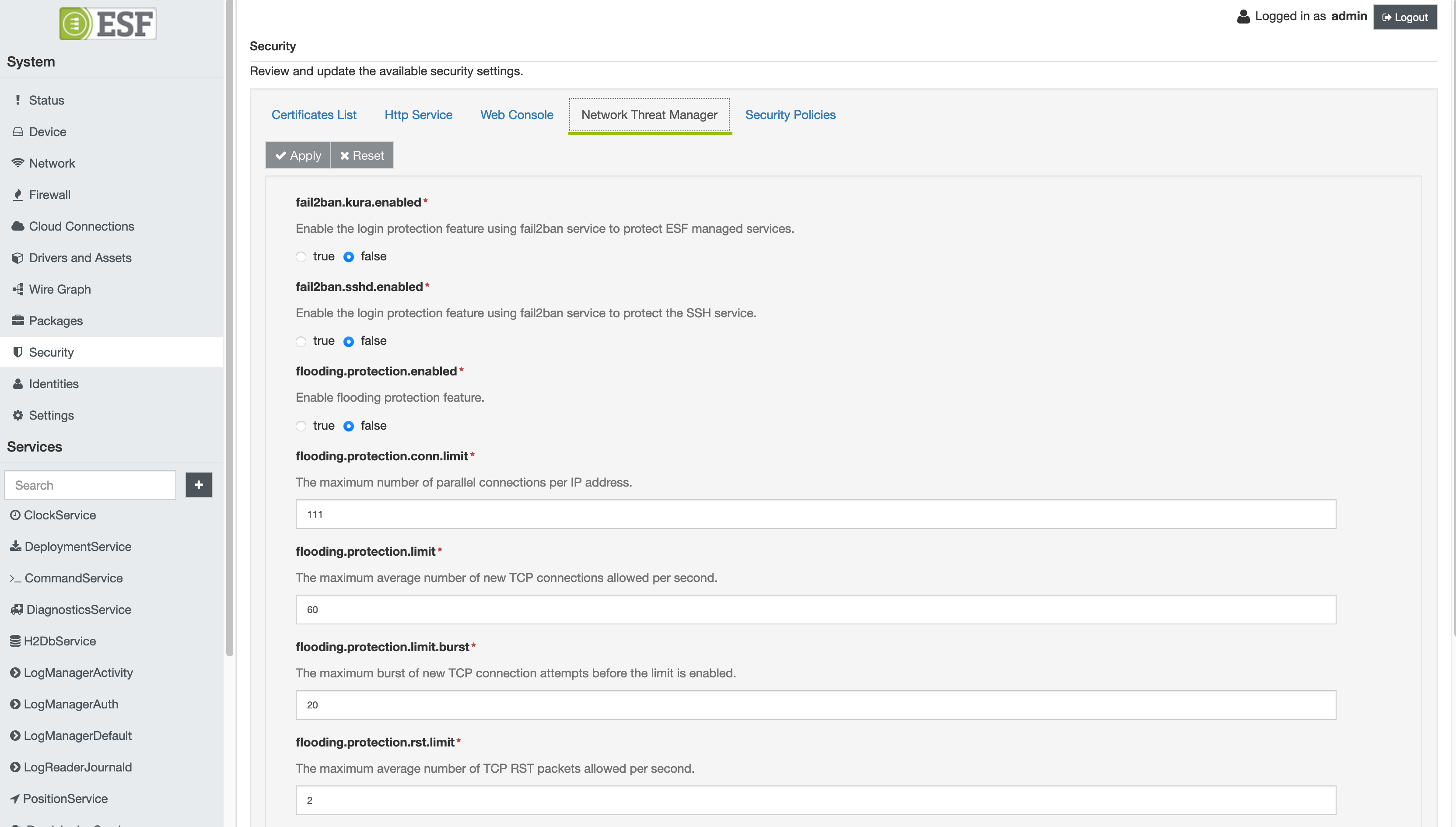
ESF provides a set of features to detect and prevent network attacks. The Security section in the Gateway Administration Console shows the Network Threat Manager tab where is it possible to activate and configure these functions.
The Network Threat Manager tab is not available for the No Network version of ESF.
The following functions are supported:
- Flooding protection
- Fail2Ban
### Flooding protection
The flooding protection function is used to prevent DDos (Distributed Denial-of-Service) attacks using a set of firewall rules. The rules affect the filter and mangle firewall tables.
The following rules are added to the mangle table and they are implemented to block invalid or malicious network packets:
iptables -A prerouting-kura -m conntrack --ctstate INVALID -j DROP
iptables -A prerouting-kura -p tcp ! --syn -m conntrack --ctstate NEW -j DROP
iptables -A prerouting-kura -p tcp -m conntrack --ctstate NEW -m tcpmss ! --mss 536:65535 -j DROP
iptables -A prerouting-kura -p tcp --tcp-flags FIN,SYN FIN,SYN -j DROP
iptables -A prerouting-kura -p tcp --tcp-flags SYN,RST SYN,RST -j DROP
iptables -A prerouting-kura -p tcp --tcp-flags FIN,RST FIN,RST -j DROP
iptables -A prerouting-kura -p tcp --tcp-flags FIN,ACK FIN -j DROP
iptables -A prerouting-kura -p tcp --tcp-flags ACK,URG URG -j DROP
iptables -A prerouting-kura -p tcp --tcp-flags ACK,FIN FIN -j DROP
iptables -A prerouting-kura -p tcp --tcp-flags ACK,PSH PSH -j DROP
iptables -A prerouting-kura -p tcp --tcp-flags ALL ALL -j DROP
iptables -A prerouting-kura -p tcp --tcp-flags ALL NONE -j DROP
iptables -A prerouting-kura -p tcp --tcp-flags ALL FIN,PSH,URG -j DROP
iptables -A prerouting-kura -p tcp --tcp-flags ALL SYN,FIN,PSH,URG -j DROP
iptables -A prerouting-kura -p tcp --tcp-flags ALL SYN,RST,ACK,FIN,URG -j DROP
iptables -A prerouting-kura -p icmp -j DROP
iptables -A prerouting-kura -f -j DROPThe following rules, instead, are added to the filter table and they are intended to limit the number of incoming TCP connections:
iptables -A input-kura -p tcp -m connlimit --connlimit-above KURA_CONN_LIMIT -j REJECT --reject-with tcp-reset
iptables -A input-kura -p tcp --tcp-flags RST RST -m limit --limit KURA_RST_LIMIT/s --limit-burst KURA_RST_BURST_LIMIT -j ACCEPT
iptables -A input-kura -p tcp --tcp-flags RST RST -j DROP
iptables -A input-kura -p tcp -m conntrack --ctstate NEW -m limit --limit KURA_LIMIT/s --limit-burst KURA_BURST_LIMIT -j ACCEPT",
iptables -A input-kura -p tcp -m conntrack --ctstate NEW -j DROPThe KURA_CONN_LIMIT, KURA_RST_LIMIT, KURA_RST_BURST_LIMIT, KURA_LIMIT and KURA_BURST_LIMIT are parameters that the user can configure through the Administration Console.
In particular, the following parameters are available:
- flooding.protection.enabled : enables the application of the firewall rules for flooding protection;
- flooding.protection.conn.limit : sets the maximum number of parallel connections per IP address;
- flooding.protection.limit : sets the maximum average number of new TCP connections allowed per second;
- flooding.protection.limit.burst : sets the maximum burst of new TCP connection attempts before the limit is enabled;
- flooding.protection.rst.limit : sets the maximum average number of TCP RST packets allowed per second;
- flooding.protection.rst.limit.burst : sets the maximum burst of TCP RST packets before the RST limit is enabled.
Fail2Ban
Fail2ban is a tool used for intrusion detection and prevention. It scans system and ESF log files and bans the IP addresses that show some malicious signs (i.e. too many password failures, etc.). Fail2Ban is used to update firewall rules to reject the IP addresses for a specified amount of time.
The Fail2Ban feature can be enable both for ESF and ssh accesses. The fail2ban.kura.enabled parameter enables the monitoring of ESF accesses, while the fail2ban.sshd.enabled one activates the monitoring of accesses via ssh.
Updated 6 months ago
